

Welcome to IT & OT Security Intelligence
Stay updated with the latest news and research in Information Technology & Operational Technology security. Cutting-edge insights on protecting critical infrastructure.
OT refers to systems that use connected devices to monitor and control real-world physical processes — manufacturing, transportation, energy, and water management.
Threat Intelligence Briefings
Deep-dive analysis of active threat campaigns
Latest Cyber News
Updated daily — filter by category or search by keyword
China-linked APT31 targeted Russian IT contractors and government integrators using legitimate cloud services for command-and-control, hiding encrypted commands in social media profiles. Operations ran undetected from 2022–2025 using SharpADUserIP, CloudSorcerer, PlugX, and Tailscale VPN.
APT24 (Pitty Tiger) deployed BADAUDIO — a DLL-hijacking C++ downloader delivering AES-encrypted Cobalt Strike. Breached a Taiwanese digital marketing firm to hijack 1,000+ domains. Uses FingerprintJS for victim targeting and avoids all mobile devices in evasion strategy.
New ClickFix variant uses full-screen fake Windows Update pages to clipboard-inject malicious commands. A multi-stage Stego Loader hides payloads inside PNG pixel data. Drops LummaC2 and Rhadamanthys infostealers using ctrampoline function chains that bypass all major EDR solutions.
Survey of 340 internet-adjacent OT environments found 112 with direct management interface exposure. Default credentials unrotated on 67% of sampled PLCs. Vulnerable firmware creates viable pathways for kinetic disruption of physical industrial operations at critical infrastructure sites globally.
A digitally-signed enterprise backup software update contained a stealthy dropper. After a 96-hour dwell period, BlackMesh ransomware was deployed with encrypted C2 via legitimate cloud infrastructure. Stolen code-signing certificate valid until 2027 used to bypass security controls. 38 organisations impacted.
Threat actors systematically disable logging subsystems and abuse WMI subscriptions + legitimate Remote Management & Monitoring tools as persistent backdoors. Average dwell time across 14 confirmed cases: 200+ days before detection. Enterprises with no anomaly detection baselines most at risk.
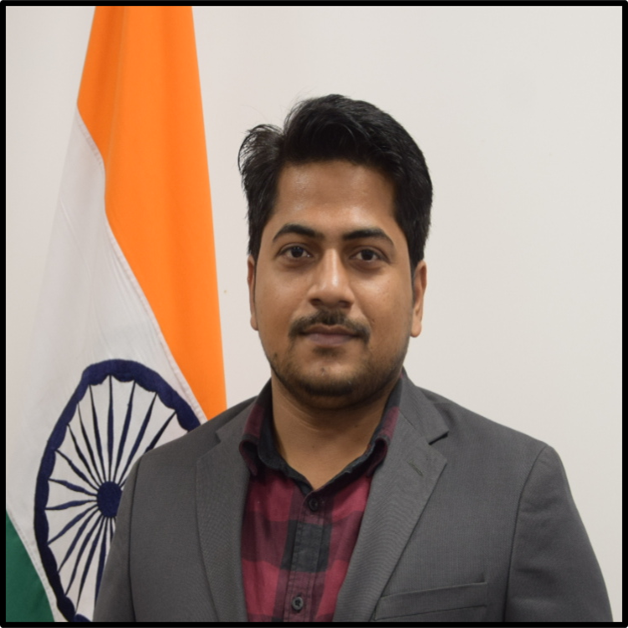
Dr. Manish Kumar Rai:
Researcher in IT & OT Security
Welcome to my platform for sharing the latest news and research in IT & OT security. With a passion for safeguarding critical infrastructure and a commitment to advancing the cybersecurity landscape, I provide valuable insights and research through this site.
Currently serving as Cybersecurity Expert at UP State Institute of Forensic Science. Previously — Assistant Professor, Center Head of OT and Cyber Defense Center at Rashtriya Raksha University. Doctoral thesis completed exclusively in Operational Technology Security. Contributor to national and international cybersecurity projects.
Stay Ahead in OT Security with Insights & Cutting-Edge Research
Gain access to comprehensive knowledge and stay informed about the latest trends, threats, and innovations in operational technology security. Our in-depth analysis provides practical insights, best practices, regulatory compliance guidance, and effective security measures tailored to your needs.
- Latest Updates & Real-Time Threat Intelligence
- Practical Guidance & Hands-On OT Training
- Regulatory Compliance — IEC 62443, NIST, ISO 27019
- Community Engagement & Research Collaboration
- Asset and Configuration Management
- Network and Access Control
- Monitoring, Detection & Incident Response
- Risk and Compliance Management
- Patch, Backup and Recovery Management
- Physical Security, Training & Threat Intelligence
Recent Activity & Deployments
Site visits, OT hardware demos and live exercises

Assessing SCADA and OT systems that control and monitor the electrical grid. Evaluated cyber threat exposure, segmentation, and access control protocols at a major power utility.

Hands-on practical OT hardware demonstration covering PLCs, RTUs, HMI interfaces and industrial communication protocols used in manufacturing, energy and transportation sectors.

The UP Anti-Terrorist Squad focusing on cybercrime including dark web investigations, drone threat analysis, and cyber forensics as part of counter-terrorism and digital intelligence operations.
Frequently Asked Questions
OT & IT security expertise — click to expand
Operational Technology (OT) cybersecurity safeguards hardware, software, networks, and systems that monitor and control industrial processes in critical infrastructure. Unlike IT security which focuses on data, OT security prioritises the availability, safety, and integrity of physical operations — a breach can cause real-world physical damage.
Key steps: Network Segmentation between IT and OT zones, Secure Remote Access with MFA, Robust Access Controls, Continuous Anomaly Monitoring, Vulnerability Management & Patch cycles, Employee Awareness Training, and documented Incident Response Planning with OT-specific playbooks.
Yes — a complete OT training package with hands-on demonstrations and setup of a Portable Operational Demo (POD) unit. The programme covers ICS/SCADA fundamentals, industrial protocols (Modbus, DNP3, OPC-UA), and OT cybersecurity best practices designed for real-world skills development.
We implement: ICS-specific firewalling and network segmentation, Asset visibility and anomaly detection, Regular backup, patch management and access controls, Real-time monitoring and OT incident response plans. We also conduct simulated and live-fire attack scenarios to test operational resilience.
Yes — full OT security audits including risk assessment, vulnerability identification, and compliance checks for ICS/SCADA environments. Audits align with IEC 62443, NIST CSF, and ISO 27019 standards, ensuring comprehensive critical infrastructure protection with a written report and remediation roadmap.
Yes — customised cyber safety training covering: safe digital practices, phishing awareness, password hygiene, secure communication and data protection. Delivered onsite or online with interactive sessions, real-world case studies, and live demonstrations. Tailored to government, corporate, and academic audiences.
Initial response within minutes for critical incidents via real-time monitoring and alerting systems. Full incident analysis and containment typically initiated within 1–2 hours. Our team handles both OT and IT environments efficiently, minimising downtime and operational impact through pre-established runbooks.
Check for: Network segmentation between IT and OT, up-to-date asset inventory and vulnerability assessments, strong access control with authentication, continuous monitoring for anomalies and incident response readiness, and compliance with IEC 62443 or NIST. We offer OT assessments to identify and remediate all gaps.
